Instant Management & Control
According to analyst predictions, by 2013, 95% workers in major corporations will use instant messaging (IM) devices as a primary business communication tool. Among their tangible advantages, users enjoy a lot of speed, immediacy and user-friendliness when exchanging information with co-workers, partners and suppliers.
However, there is a downside to the productivity benefits of IM applications. Left unchecked, they become a huge security nightmare to the organization due to lack of audit trail on chat conversations, susceptibility to eavesdropping, possible routes for malware and data leakage and loss of working hours to chatting.
Cyberoam Instant Messaging Control
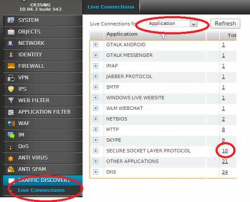
Cyberoams Instant Messaging Control empowers the administrator to gain control on various IM applications used in an organization, and prevent data loss through them. By monitoring and controlling all data transferred over these applications, organizations can overcome their wariness in embracing public IM applications for business productivity.
Key Benefits:
- Preventing employees from idle chat
- Block file transfers, audio, videos, games
- Malware-free
- Granular restriction of IM privileges between individual users and groups
- Keyword-based content filtering
- Saving bandwidth on VOIP calls, webcam use
Administrators can use Cyberoam Instant Messaging Controls identity-based property to achieve the following aims: obtaining logs of all Yahoo/Windows Live messenger communication between users, imposing granular controls on who can chat with whom in the organization, blocking file transfers and audio/video/webcam chat access (restricting users to text chat only), preventing data loss in the organization through files uploaded on IM, sending access denied messages for user education and preventing music downloads and online games.
The IM Control rule can be easily configured from the Cyberoam Web GUI and takes just a few seconds.
IM Contact
The IM Contact section is an identity-based feature which can be used to register contact details of various messaging application users. A contact can be created for a user as well as a group of users by simply adding any valid Yahoo or MSN email IDs. This is a deterrent to the threat of ex-employees using multiple aliases to extract sensitive information from the organization.
Administrators can easily view a complete list of multiple contact groups for swift action.
IM Rules
The IM rules feature is used to enforce chat privileges for various users and groups by setting pre-defined policies to permit IM communications based on the following parameters:
- Conversation privileges Chat conversation is allowed / denied between various identities. This is very useful to discourage idle chatters.
- Login Configuring and managing login rules based on username or IM contact name
- File transfer Granularly restricting file transfer between any two identities
- Webcam Configuring and managing webcam rules between any two identities
Content Filtering over IM
Cyberoams instant messaging content filtering feature allows administrator to blacklist certain keywords and regular expressions which may pose a security concern. Each time a user types those banned keywords, an error message is displayed on the screen. Educational institutes are able to use this feature to block profane language among kids whereas organizations can use it to define privacy policies guidelines for business chat.